Soal Latihan RCSP-W (Part 2)
Lanjutan dari sini
11. What happens to traffic when a Steelhead appliance reports admission control?
A. Traffic will be interrupted
B. The Steelhead stops the interception of new connection for optimization for as long as it is in admission control
C. This is just a report and the Steelhead will continue to optimize traffic
D. The Steelhead will start optimizing faster any new connections
E. The Steelhead will shut down in less than a minute
Answer: B
12. Can you optimize FTP using Steelhead Mobile?
A. Yes, this is possible on all FTP modes
B. When using active FTP
C. When using passive FTP
D. It is not possible to optimize FTP traffic
E. Only when there is no firewall enabled
Answer: C
13. In a quad Interceptor appliance deployment the directly connected pairs are configured in failover mode
IC-A & IC-B are failover buddies
IC-C & IC-D are failover buddies
To prevent asymmetric routing IC-A should be configured to have a neighbor relationship with which of the following peer Interceptors?
(Select 2)
A. IC-B
B. IC-C
C. IC-D
D. Interceptor appliance uses auto discovery to learn about each other
E. Neighbor relationships are unnecessary in a quad Interceptor appliance deployment
Answer: B, C
14. When configuring SSL optimization for Steelhead Mobile clients, what step must be taken?
A. Mutual exchange of public keys between the Steelhead Mobile Controller and the Server-side Steelhead appliance
B. Mutual exchange of private keys between the Steelhead Mobile Controller and the server-side Steelhead appliance
C. Generate a self-signed certificate for the Steelhead Mobile Controller and import that on the client PCs
D. Import the server’s public and private keys to the Steelhead Mobile Controller
E. Generate individual certificates for each PC and manually import the public key on the Steelhead Mobile Controller
Answer: A
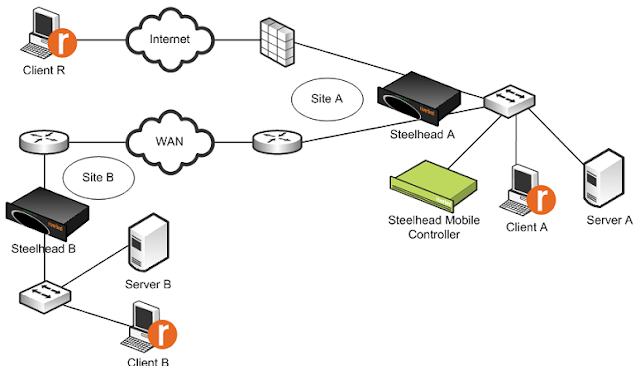
15. What option in the Acceleration policy used on Steelhead Mobile Client A will most likely enhance the users experience connecting to Server B, if Server B is an Exchange 2003 Server?
A. Enable MAPI NSPI
B. Increase the datastore size
C. Enable latency-based location awareness
D. Enable SSL optimization and import the Exchange certificate for Server B into Steelhead B
E. Peering rule rejecting optimization with Steelhead A
Answer: C
- Acceleration Policy –configuration template for groups of clients that have the same performance requirements
- Latency-detection location awareness – enables the Mobile Clients to optimize data only if latency to the closest Steelhead appliance is greater than the threshold value. The default latency threshold value is 10 ms. To configure the value on the Mobile Controller, select Policies > Location Awareness.
16. What service needs to be allowed if you are enforcing outbound security in the Steelhead Mobile solution?
A. rbtdebug.exe
B. rbtmon.exe
C. shmobile.exe
D. rbtsport.exe
E. All of the above
Answer: E
If you are enforcing outbound security, your firewall must allow the following client application components:
• For Windows- rbtdebug.exe, rbtmon.exe, shmobile.exe, and rbtsport.exe
• For Mac OS X- rbtdebug, rbtmond, rbtsport, and rbtuseragentd
Referensi: Steelhead Mobile Controller Installation Guide, halaman 3
17. What type of reporting information will an Interceptor appliance store? (Select 2)
A. Connection counts
B. Total packets in and out
C. Bytes and packets redirected to each neighbor Steelhead appliance
D. Scalable Data Referencing (SDR) Status
Answer: A, B
18. You can monitor your Steelhead appliance disk performance using which reports? (Select 2)
A. Data Store Cost
B. Data Store Performance
C. Disk Load
D. SDR Hit
E. Disk Pressure
F. Disk Alarm
Answer: A, C
Disk Performance
Take disk performance into account for high-end data center deployments. Certain types of data put more load on the disk systems and can be monitored if performance issues are suspected. High throughput datareplication deployments typically use dedicated Steelhead appliances. Monitor the disk systems with the following OID.
Use the following Data Store Disk Load report in the Management Console to monitor disk performance. If the Disk Load report is showing 80-90% for a sustained amount of time, or multiple times a day that coincide with periods of lower performance and average RiOS data store cost greater than 5000, the disk load might be impacting overall performance.
19. On the Interceptor appliance, what are the possible filter settings on a load balancing rule? (Select 4)
A. Source Port
B. Source IP Subnet
C. Destination IP Subnet
D. Destination Port
E. VLAN ID
Answer: B, C, D, E
Load-balancing rules define the characteristics by which traffic is selected for load balancing and the availability of LAN-side Steelhead appliance for such traffic. Under Load Balancing Rules, configure load-balancing rules as described in the following table.
20. The Interceptor appliance can be configured to redirect traffic to the Steelhead appliances via what methods?
A. GRE
B. L2
C. ISIS
D. Multicast
E. Redirection is automatic and not configurable
Answer: E
21. By default, which Steelhead appliances are placed in an Interceptor appliance’s auto pool?
A. All Steelhead appliances in the network
B. Peer-neighbor Steelhead appliances as targets in one Load Balancing rule
C. Peer-neighbor Steelhead appliances not assigned as targets in any Load Balancing rule
D. Peer-neighbor Steelhead appliances assigned to all current Load Balancing rules
Answer: C
22. What information does the OVA package include about the Virtual Steelhead appliance? (Select 4)
A. Virtual Disks
B. CPU
C. Memory
D. License
E. Storage
Answer: A, B, C, E
The Virtual SMC for ESX image is an installable open virtual appliance (OVA) package. OVA is a platform-independent, efficient, extensible, and open packaging distribution format. The OVA package provides a complete specification for Virtual SMC for ESX, including its required virtual disks, CPU, memory, networking, and storage.
Referensi: Steelhead Mobile Controller Installation Guide, halaman 44.
23. To verifý that the Steelhead Mobile client software is running, what process should you look for in the windows Task Manager?
A. rbtsport.exe
B. taskmgr.exe
C. svchost.exe
D. services.exe
E. rivmobile.exe
Answer: A
How to check whether SH mobile client software is running or not:
a. On the client system tray, right-click and select Task Manager to open the Windows Task Manager dialog box.
b. Click Processes and look for the rbtsport.exe process.
24. It is not recommended to use the same Steelhead appliance to optimize both replication traffic and general user traffic because:
A. Replication traffic uses 16 KB blocks and causes fragmentation in the datastore
B. User traffic may contain sensitive traffic and should not be mixed with other traffic
C. Replication traffic may cause admission control therefore affecting user traffic
D. The traffic pattern between the two types of traffic is generally very different and therefore the datastore may wrap more quickly affecting performance
Answer: D
Pada SDR, jika data yang dilewatkan polanya sama, maka akan dideduplikasi dan hanya dikirimkan referensinya (warm transfer), namun jika polanya berbeda, maka yang terjadi adalah cold transfer sehingga datastore akan lebih cepat penuhnya.
25. Which of the following are Steelhead Mobile Controller alarms? (Select 2)
A. Memory paging
B. Datastore errors
C. Peer version mismatch
D. SSL errors
E. File system full
Answer: A, E
Steelhead Mobile Controller Alarms
1 . File System Full
Raise Alarm When Steelhead Mobile Controller File System is Almost Full
Specify this option to trigger an alarm when any of the disk partitions are almost full. This alarm is enabled by default.
2. Memory Paging
Raise Alarm When Extended Memory Paging Activity is Detected
Specify this option to trigger the memory paging alarm. If 100 pages are swapped every couple of hours, the Mobile Controller is functioning properly. If thousands of pages are swapped every few minutes, contact Riverbed Support.This alarm is enabled by default.
Referensi: Daftar alarm lengkapnya, lihat Steelhead Mobile User Guide, halaman 26
26. When using SSL, what is the purpose of peer authentication?
A. Register peers
B. Confirm the identity of the peer
C. Establish sessions
D. verify the user permissions
E. Authenticate the client to the server
Answer: B
27. For In-path rules on an Interceptor appliance, Source and Destination subnets are specified in what format? (where “x’ is any single digit number):
A. xxx.xxx.xxx netmask xxx.xxx.xxx
B. xxx.xxx.xxx.xxx/xx
C. “all subnets”
D. Xxx.xxx.xxx.xxx.xx
Answer: B
28. What are the SSL trusts that must be configured for a Steelhead Mobile client to successfully optimize SSL traffic? (Select 2)
A. Steelhead Mobile clients trust Steelhead Mobile Controller
B. Server-side Steelhead trust Steelhead Mobile Clients
C. Steelhead Mobile clients trusts client-side Steelhead
D. Client-side Steelhead, server-side Steelhead, Steelhead Mobile clients, and CMC appliance all must trust each other
Answer: A, B
29. A deployment has two parallel Interceptor appliances (A and B) each across a different link directed at different data center locations. Each data center has one Steelhead appliance (Steelhead-1 or Steelhead-2). The administrator wants probes coming into Interceptor A to be first serviced by Steelhead-1 , then Steelhead-2 only if Steelhead-1 is full or unavailable. What is the most appropriate rule to be configured?
A. A Redirect Load Balancing rule containing Steelhead-1 and Steelhead-2
B. No Load Balancing rules are needed for the administrator’s policy
C. Two Redirect Load Balancing rules, first rule for Steelhead-1 and second rule for Steelhead-2
D. Two Redirect Load Balancing rules; first for both Steelhead-1 and Steelhead-2, second one for Steelhead-2
Answer: C
30. On the Steelhead Mobile Controller, when should you use the CIFS option “Disable Write Optimization”?
A. When the Steelhead Mobile client does frequent writes to large files
B. An application that expect write-through without asking for it explicitly
C. To increase performance during large updates to files
D. To reduce datastore usage on busy Steelhead Mobile clients
E. To increase performance during directory listings
Answer: B
When a client wants to write data to a file, there are two modes of writing that are supported in CIFS environments: write-through and write-back. The application using CIFS can decide which of these two modes to use every time it needs to write. For write-through mode, the process falls into a pattern in which the client sends data to the server for writing, waits for an acknowledgment from the server, sends some more data, waits, and so on, until all the data is written and acknowledged. At this point the client sends a CIFS command to close the file on the server. The acknowledgement from the server that the file is closed signals that all data is safely written to disk. The server releases any lock on the file and makes it available for read-write access to other clients. Although this might be the safest way when writing data, when sending data across the WAN, it is not the most efficient method because the round-trip time across the WAN is typically several magnitudes higher than across the LAN.
Referensi: Steelhead Appliance Deployment Guide – Protocols, halaman 10.
InsyaAllah masih ada sambungannya lagi… (Banyak soalnya euy)